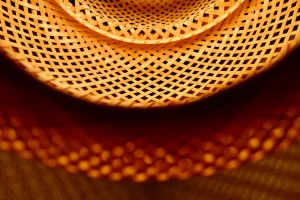
Device securityThe access doors to the data
Endpoint Protection is essential to ensure that the devices provided to employees and collaborators can deliver maximum connectivity and productivity performance without posing a risk to the data they contain and the networks they access. Today, in fact, personal devices have become real doors, through which valuable information passes in flows that are increasingly complex to monitor and, consequently, to protect: cyber criminals see these doors as an opportunity to launch targeted attacks


A new approach to endpoint protectionProtecting PC and Server
Intrusion Detection System sensors receive information from the network and transmit it to an engine that analyzes it for flaws in computer security, identifying data packets, anomalies and activities that violate the rules set by network administrators jointly with Security Managers.

Traditional systems
It tends to be the case that antivirus software is used to protect devices from intrusions and malware. Antivirus software works according to the logic of signature comparators: a defense is effective if the signature database is constantly updated. This method shows several limitations in the current scenario, which is characterized by the continuous appearance of new threats.
Endpoint detection & response
This is why WIIT offers its customers Endpoint Detection & Response (EDR) solutions that use the cloud, threat intelligence and highly specialized resources to guarantee advanced and dynamic protection of PCs and servers. Only through EDR solutions can attacks be identified and blocked in near real-time.


Here comes the intelligent defense
In fact, in the event of suspicious activity, the EDR intersects local resources with available information on the cloud in real time, leveraging threat intelligence to correlate information and make decisions that counter identified threats, blocking the affected location if certain risk levels are exceeded.
Considering also the human element
Endpoint defense also depends on end user behaviour. For this, the EDR leverages specific risk indicators and Threat Intelligence feeds to evaluate the actions taken by the end-user, sending notifications in case of conduct that could compromise the security of the device.